 A FAFF file is a file that uses the `.faff` extension, but unlike familiar formats such as PDF, DOCX, JPG, or MP3, it does not appear to be a widely recognized standard file type. In practical terms, that means it is probably not a format that many different programs are built to open automatically. Common formats are widely supported because their structure is publicly documented or broadly understood, allowing many applications to read them. A FAFF file, by contrast, is more likely tied to a specific piece of software, which is why simply seeing the extension does not immediately tell you exactly what kind of content it holds.
A FAFF file is a file that uses the `.faff` extension, but unlike familiar formats such as PDF, DOCX, JPG, or MP3, it does not appear to be a widely recognized standard file type. In practical terms, that means it is probably not a format that many different programs are built to open automatically. Common formats are widely supported because their structure is publicly documented or broadly understood, allowing many applications to read them. A FAFF file, by contrast, is more likely tied to a specific piece of software, which is why simply seeing the extension does not immediately tell you exactly what kind of content it holds.
When a file type is not a common public format, it usually means the format is not broadly used or openly standardized in the same way as mainstream file types. Instead of being designed for universal compatibility, it may have been created for the internal needs of one program, one company, or one workflow. In that situation, the extension acts more like a label used by that software to identify its own files. This is why an uncommon extension such as `.faff` may not be recognized by Windows or by common third-party viewers, converters, or editors. The file may only make proper sense when opened by the original application that created it.
This is also why a FAFF file is often described as a proprietary or application-specific data file. That phrase means the file is likely meant to store information for a particular program rather than serve as a general-purpose document, image, or media file. It could contain settings, project data, saved work, structured records, or other information that the software needs in order to load, continue, or manage a task. Because the structure is often defined by the program itself, other applications may not know how to interpret the contents correctly.
Even so, an uncommon file extension does not automatically mean the contents are completely unreadable. Some programs save data using text-based structures such as XML or JSON, even when they assign the file a custom extension. In those cases, opening the file in a text editor might reveal readable clues such as names, dates, file paths, settings, version information, or labeled data fields. If the file was stored in a binary format instead, however, it will usually appear as random or broken characters in a text editor. That does not necessarily mean the file is damaged; it simply means the data was encoded for software interpretation rather than human reading.
If you do not know what program created the FAFF file, the best clue is often the file’s origin rather than the extension itself. It helps to look at where the file came from, such as an email attachment, a website download, a folder created by a certain application, or another computer where specific software was installed. The surrounding context often reveals more than the extension alone. In many cases, identifying the application that produced the file is the key to understanding what the file is and how it should be opened. In short, a FAFF file is most likely a specialized file associated with a particular program, and the original software that created it is usually the safest and most reliable way to open or interpret it If you liked this report and you would like to get more details pertaining to FAFF file viewer software kindly check out our web-page. .


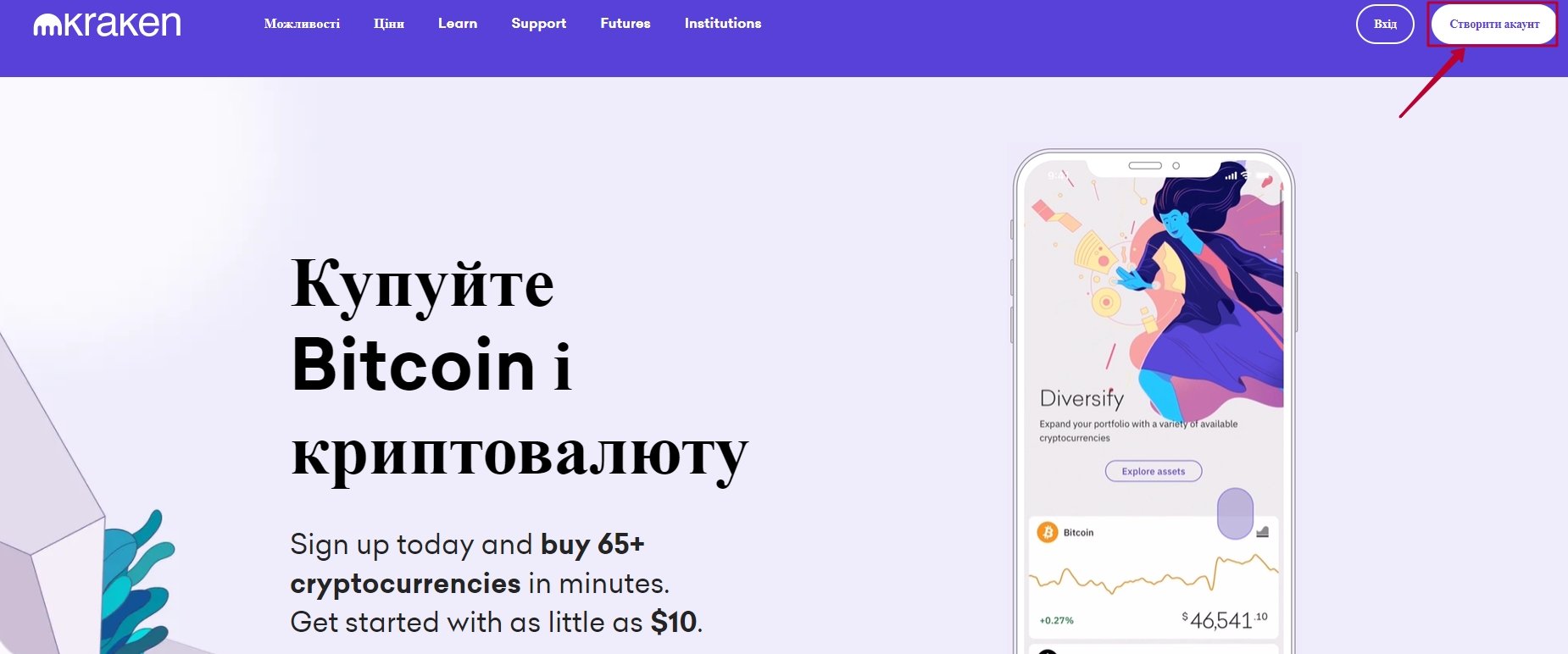 Важные меры безопасности при работе с KRAKEN:
Важные меры безопасности при работе с KRAKEN: